How to obtain an A+ in the Qualys SSL Labs Security Test: Difference between revisions
| Line 11: | Line 11: | ||
This wiki requires using the CLI as some options are not available via the Admin Console. '''Please note''': obtaining the best results via the SSL Labs test may not align with your business requirements or environment (e.g. you are still running old equipment like Windows XP, use older Java clients, etc.). Tune your environment according to your needs. | This wiki requires using the CLI as some options are not available via the Admin Console. '''Please note''': obtaining the best results via the SSL Labs test may not align with your business requirements or environment (e.g. you are still running old equipment like Windows XP, use older Java clients, etc.). Tune your environment according to your needs. | ||
=== [[Security/Collab/87|Zimbra Collaboration 8.7]] === | === [[Security/Collab/87|Zimbra Collaboration 8.7.x]] === | ||
ZCS 8.7 defaults to using a 2048-bit DH parameter ([https://bugzilla.zimbra.com/show_bug.cgi?id=99558 bug 99558]) which come from [http://tools.ietf.org/html/rfc3526#page-3 RFC3526 IKE 2048-bit PEM (group 14)] for anything in ZCS that utilizes OpenSSL. | ZCS 8.7.x defaults to using a 2048-bit DH parameter ([https://bugzilla.zimbra.com/show_bug.cgi?id=99558 bug 99558]) which come from [http://tools.ietf.org/html/rfc3526#page-3 RFC3526 IKE 2048-bit PEM (group 14)] for anything in ZCS that utilizes OpenSSL. | ||
==== Custom or Stronger DH Parameters ==== | ==== Custom or Stronger DH Parameters ==== | ||
In 8.7 you can generate new/custom DH parameters using a new utility '''zmdhparam''' which calls openssl dhparam. | In 8.7.x you can generate new/custom DH parameters using a new utility '''zmdhparam''' which calls openssl dhparam. | ||
zmdhparam set -new 2048 | zmdhparam set -new 2048 | ||
or | or | ||
Revision as of 00:40, 12 February 2017
How to obtain an A+ in the Qualys SSL Labs security test
Purpose
List the steps, per release, to obtain an A+ in the Qualys SSL Labs Security Test.
Resolution
This wiki requires using the CLI as some options are not available via the Admin Console. Please note: obtaining the best results via the SSL Labs test may not align with your business requirements or environment (e.g. you are still running old equipment like Windows XP, use older Java clients, etc.). Tune your environment according to your needs.
Zimbra Collaboration 8.7.x
ZCS 8.7.x defaults to using a 2048-bit DH parameter (bug 99558) which come from RFC3526 IKE 2048-bit PEM (group 14) for anything in ZCS that utilizes OpenSSL.
Custom or Stronger DH Parameters
In 8.7.x you can generate new/custom DH parameters using a new utility zmdhparam which calls openssl dhparam.
zmdhparam set -new 2048
or
zmdhparam set -new 3072
Tune the Cipher list
As zimbra, run the next command to tune the Ciphers and disable the RC4, etc:
zmprov mcf zimbraReverseProxySSLCiphers 'ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-DSS-AES128-GCM-SHA256:kEDH+AESGCM:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA:ECDHE-ECDSA-AES256-SHA:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:DHE-DSS-AES128-SHA256:DHE-RSA-AES256-SHA256:DHE-DSS-AES256-SHA:DHE-RSA-AES256-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128:AES256:HIGH:!aNULL:!eNULL:!EXPORT:!DES:!MD5:!PSK:!RC4'
Restart the proxy:
zmproxyctl restart
Strict Transport Security (HSTS) & Session resumption (caching)
Run the next command to add the proper headers to the configuration:
zmprov mcf +zimbraResponseHeader "Strict-Transport-Security: max-age=31536000"
Restart the zimbra services
zmcontrol restart
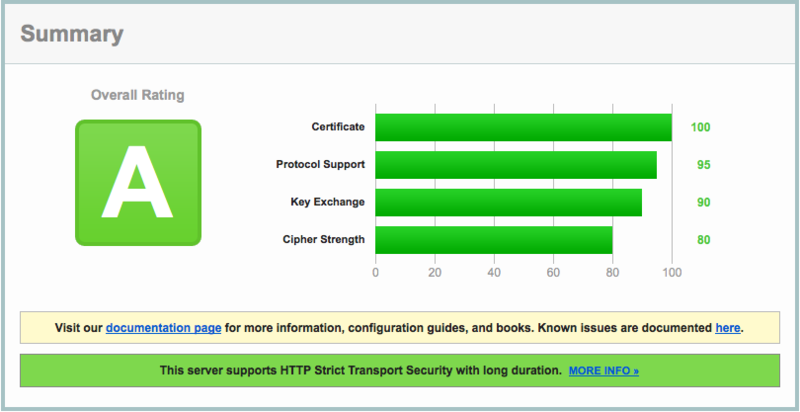
The result
The result in the SSL Labs test will be:
Zimbra Collaboration 8.6 & 8.5
Using Proxy
Fix the Logjam issue
ZCS 8.6 has a default 1024-bit DH parameter. Best practice is to use at least 2048-bit and that is the minimum for an A+ with Qualys SSL Labs.
As zimbra, create a new 2048 key (it make take several minutes):
openssl dhparam -out /opt/zimbra/conf/dhparam.pem 2048
Edit the following two files:
/opt/zimbra/conf/nginx/templates/nginx.conf.web.https.default.template /opt/zimbra/conf/nginx/templates/nginx.conf.web.https.template
Add a ssl_dhparam entry before the include so that you end up with something like the following:
ssl_verify_client ${ssl.clientcertmode.default};
ssl_verify_depth ${ssl.clientcertdepth.default};
ssl_dhparam /opt/zimbra/conf/dhparam.pem;
include ${core.includes}/${core.cprefix}.web.https.mode-${web.mailmode};
Tune the Cipher list
As zimbra, run the next command to tune the Ciphers and disable the RC4, etc:
zmprov mcf zimbraReverseProxySSLCiphers 'ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-DSS-AES128-GCM-SHA256:kEDH+AESGCM:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA:ECDHE-ECDSA-AES256-SHA:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:DHE-DSS-AES128-SHA256:DHE-RSA-AES256-SHA256:DHE-DSS-AES256-SHA:DHE-RSA-AES256-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128:AES256:HIGH:!aNULL:!eNULL:!EXPORT:!DES:!MD5:!PSK:!RC4'
Restart the proxy
zmproxyctl restart
Strict Transport Security (HSTS)
As zimbra, edit these files:
/opt/zimbra/conf/nginx/templates/nginx.conf.web.https.default.template /opt/zimbra/conf/nginx/templates/nginx.conf.web.https.template
and add the following in the server { ... } section:
add_header Strict-Transport-Security "max-age=31536000";
Session resumption (caching)
As zimbra, add the following content after the add_header that you added in the previous step:
ssl_session_cache shared:SSL:50m; ssl_session_timeout 5m;
As zimbra, restart the proxy:
zmproxyctl restart
The result
The result in the SSL Labs test will be:
Without Proxy
Thank you to Alex that wrote these steps months ago.
Fix the Logjam issue
At this moment, Zimbra can't provide any solution to fix Logjam in Zimbra Collaboration 8.5 or above without use Proxy in front, please install the Proxy role. Also you can disable the next Cipher plus the next section to avoid logjam, but all the DHE Cipher will be disabled and can cause some troubles:
zmprov mcf +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_WITH_AES_128_CBC_SHA zmprov mcf +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_WITH_AES_128_CBC_SHA256 zmprov mcf +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_WITH_AES_128_GCM_SHA256
Tune the Cipher list
As user zimbra, run the next command to tune the Ciphers and disable the RC4, etc:
zmprov mcf +zimbraSSLExcludeCipherSuites SSL_DHE_DSS_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_DSS_WITH_DES_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_RSA_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_RSA_WITH_3DES_EDE_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_RSA_WITH_DES_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_RSA_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_RSA_EXPORT_WITH_RC4_40_MD5 \ +zimbraSSLExcludeCipherSuites SSL_RSA_WITH_3DES_EDE_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_RSA_WITH_DES_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_RSA_WITH_RC4_128_MD5 \ +zimbraSSLExcludeCipherSuites SSL_RSA_WITH_RC4_128_SHA \ +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_ECDHE_RSA_WITH_RC4_128_SHA \ +zimbraSSLExcludeCipherSuites TLS_RSA_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_3DES_EDE_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_AES_128_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_AES_128_CBC_SHA256 \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_AES_128_GCM_SHA256 \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_DES_CBC_SHA
Restart the mailbox service
zmmailboxdctl restart
Strict Transport Security (HSTS)
As zimbra edit the file /opt/zimbra/jetty/etc/jetty.xml.in and search by:
<Call name="addRule">
<Arg>
<New class="org.eclipse.jetty.rewrite.handler.RewritePatternRule">
<Set name="pattern">/Microsoft-Server-ActiveSync/*</Set>
<Set name="replacement">/service/extension/zimbrasync</Set>
</New>
</Arg>
</Call>
Add the following just before that entry:
<Call name="addRule">
<Arg>
<New class="org.eclipse.jetty.rewrite.handler.HeaderPatternRule">
<Set name="pattern">*</Set>
<Set name="name">Strict-Transport-Security</Set>
<Set name="value">max-age=15768000; includeSubDomains</Set>
</New>
</Arg>
</Call>
Restart the mailbox service
zmmailboxdctl restart
The result
The result if you followed all the previous steps in the SSL Labs test will be:
If the Logjam steps were not performed, you will obtain a B.
Zimbra Collaboration 8.0.9
Generate a SSL Certificate with SHA256
By default, ZCS 8.0.x generated CSRs with SHA1 instead of the now preferred SHA256 hash. Edit /opt/zimbra/bin/zmcertmgr as root to change the default.
Change this line:
${openssl} req -new -${DIGEST} -nodes -out ${current_csr} -keyout ${current_key} \
To the following (adding the -sha256 to the openssl command):
${openssl} req -sha256 -new -${DIGEST} -nodes -out ${current_csr} -keyout ${current_key} \
Use the Administration Console and CLI Certificate Tools to generate the new CSR (now with a SHA256 hash).
Disable SSLv3 to fix POODLE
Follow How to disable SSLv3 to disable SSLv3 in your ZCS 8.0.x environment.
Disable Client-Initiated SSL renegotiation
Edit the Jetty template and search by org.eclipse.jetty.server.ssl.SslSelectChannelConnector. Before the Set name="Port" line, add a allowRenegotiate False as follows:
<New id="ssl" class="org.eclipse.jetty.server.ssl.SslSelectChannelConnector">
<Set name="allowRenegotiate">FALSE</Set>
<Set name="Port">%%zimbraMailSSLPort%%</Set>
Restart the mailbox service
zmmailboxdctl restart
Strict Transport Security (HSTS)
Add the proper header to the configuration:
zmprov mcf +zimbraResponseHeader "Strict-Transport-Security: max-age=31536000"
Restart the zimbra services
zmcontrol restart
Using Proxy
The first step you need to check if you are using the proxy (nginx) or just mailboxd (jetty):
1. Verify if nginx is listening on port 443, in this case you can see that is jetty and not nignx:
lsof -i :443 COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME java 6637 zimbra 96u IPv4 198165 0t0 TCP *:https (LISTEN)
2. Enable nginx for https, for POP3 and IMAP reverseproxy, as zimbra user:
./libexec/zmproxyconfig -e -w -o -a 8080:80:8443:443 -x https -H `zmhostname` ./libexec/zmproxyconfig -e -m -o -i 7143:143:7993:993 -p 7110:110:7995:995 -H `zmhostname`
3. Sanity check #1
zmprov gs `zmhostname` zimbraMailReferMode # name zimbra8.zimbra.io zimbraMailReferMode: reverse-proxied
4. Sanity check #2
lsof -i :443 COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME nginx 31418 zimbra 10u IPv4 314934 0t0 TCP *:https (LISTEN) nginx 31419 zimbra 10u IPv4 314934 0t0 TCP *:https (LISTEN) nginx 31420 zimbra 10u IPv4 314934 0t0 TCP *:https (LISTEN) nginx 31421 zimbra 10u IPv4 314934 0t0 TCP *:https (LISTEN)
Now you have nginx properly enabled.
Fix the Logjam issue
Zimbra 8.0.x has a default 1024-bit DH parameter. Best practice is to use at least 2048-bit and that is the minimum for an A+ with Qualys SSL Labs.
As zimbra, create a new 2048 key (it make take several minutes):
openssl dhparam -out /opt/zimbra/conf/dhparam.pem 2048
Edit the following two files:
/opt/zimbra/conf/nginx/templates/nginx.conf.web.https.default.template /opt/zimbra/conf/nginx/templates/nginx.conf.web.https.template
Add a ssl_dhparam entry before the include so that you end up with something like the following:
ssl_verify_client ${ssl.clientcertmode.default};
ssl_verify_depth ${ssl.clientcertdepth.default};
ssl_dhparam /opt/zimbra/conf/dhparam.pem;
include ${core.includes}/${core.cprefix}.web.https.mode-${web.mailmode};
Disable weak Ciphers
Disable weak Ciphers, thank you to ShanxT. Please note, by eliminating these ciphers, some older clients may stop working:
zmprov mcf +zimbraSSLExcludeCipherSuites TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 \ +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_WITH_AES_256_CBC_SHA \ +zimbraSSLExcludeCipherSuites DHE-RSA-AES256-SHA \ +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_WITH_AES_256_CBC_SHA256 \ +zimbraSSLExcludeCipherSuites DHE-RSA-AES256-SHA256 \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_AES_256_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_RSA_WITH_DES_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_RSA_WITH_DES_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_DSS_WITH_DES_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_RSA_EXPORT_WITH_RC4_40_MD5 \ +zimbraSSLExcludeCipherSuites SSL_RSA_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_RSA_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_DSS_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_WITH_AES_128_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_AES_128_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_RSA_WITH_3DES_EDE_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_RSA_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_DES_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_RSA_WITH_3DES_EDE_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_WITH_AES_128_CBC_SHA256 \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_AES_128_CBC_SHA256 \ +zimbraSSLExcludeCipherSuites TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256 \ +zimbraSSLExcludeCipherSuites TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_AES_256_CBC_SHA256
Tune the Cipher list
Disable RC4 ciphers with the following command:
zmprov mcf +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_RC4_128_MD5 \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_RC4_128_SHA \ +zimbraSSLExcludeCipherSuites SSL_RSA_WITH_RC4_128_MD5 \ +zimbraSSLExcludeCipherSuites SSL_RSA_WITH_RC4_128_SHA \ +zimbraSSLExcludeCipherSuites TLS_ECDHE_RSA_WITH_RC4_128_SHA
Restart the mailbox service
zmmailboxdctl restart
The result
The result using a valid SSL commercial certificate, and ZCS 8.0.9 Proxy, in the SSL Labs test will be an A+ if you followed all the steps.
Without Proxy
Fix the Logjam issue
At this moment, Zimbra can't provide any solution to fix Logjam in Zimbra Collaboration 8.0.9, you need to upgrade to Zimbra Collaboration 8.6. But you can disable the following Ciphers, plus the next section to avoid logjam, but all the DHE Cipher will be disabled and can cause some troubles in old computers/clients:
zmprov mcf +zimbraSSLExcludeCipherSuites \ +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_WITH_AES_256_CBC_SHA \ +zimbraSSLExcludeCipherSuites DHE-RSA-AES256-SHA \ +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_WITH_AES_256_CBC_SHA256 \ +zimbraSSLExcludeCipherSuites DHE-RSA-AES256-SHA256 \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_AES_256_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_RSA_WITH_DES_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_RSA_WITH_DES_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_DSS_WITH_DES_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_RSA_EXPORT_WITH_RC4_40_MD5 \ +zimbraSSLExcludeCipherSuites SSL_RSA_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_RSA_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_DSS_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_WITH_AES_128_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_AES_128_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_RSA_WITH_3DES_EDE_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_RSA_EXPORT_WITH_DES40_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_DES_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA \ +zimbraSSLExcludeCipherSuites SSL_DHE_RSA_WITH_3DES_EDE_CBC_SHA \ +zimbraSSLExcludeCipherSuites TLS_DHE_RSA_WITH_AES_128_CBC_SHA256 \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_AES_128_CBC_SHA256 \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_AES_256_CBC_SHA256
Tune the Cipher list
As zimbra, run the following command to disable RC4 ciphers:
zmprov modifyConfig +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_RC4_128_MD5 \ +zimbraSSLExcludeCipherSuites TLS_RSA_WITH_RC4_128_SHA \ +zimbraSSLExcludeCipherSuites SSL_RSA_WITH_RC4_128_MD5 \ +zimbraSSLExcludeCipherSuites SSL_RSA_WITH_RC4_128_SHA \ +zimbraSSLExcludeCipherSuites TLS_ECDHE_RSA_WITH_RC4_128_SHA
Restart the mailbox service
zmmailboxdctl restart
The result
The result, using a valid SSL commercial certificate and Zimbra Collaboration Single-Server 8.0.9 without Proxy, in the SSL Labs test will be an A if you followed all the steps. If you want to obtain the A+, please upgrade to Zimbra Collaboration 8.6 with Proxy:
Additional Content
- Thank you to http://managedhosting.de for the original wiki about disable logjam - https://wiki.zimbra.com/wiki/Security/Collab/logjam
- Thank you to Irontec to wrote the next Blog entry about how to generate CSR with hash SHA256.